Sharing wallet information introduces immediate financial risk and privacy gaps. Weak protections, insecure APIs, and social engineering can expose data or enable unauthorized transfers. Shared access muddles ownership, slows revocation of permissions, and can leak activity logs. Strict access controls, least privilege, MFA, and thorough audits help mitigate these dangers, but implementation remains delicate. The implications are serious, and the next steps require careful evaluation of who can see what, and under which conditions safeguards hold.
Why Wallet Info Is High-Rakes
Wallet information carries significant risk because it grants access to funds and transaction capabilities. In this view, the information acts as a key that can unlock undue control, creating immediate financial exposure. The discussion highlights privacy gaps and evolving trust dynamics, urging vigilance. From a freedom-minded stance, users seek safeguards, transparency, and deliberate sharing practices to minimize potential harm.
How Thieves Exploit Payment Details
Thieves exploit payment details by surveying how data is stored, transmitted, and validated to identify weak links. They leverage weak encryption, flawed tokenization, and insecure APIs to access funds or personal records. Breach risk rises through server misconfigurations and outdated software. Social engineering compounds exposure, manipulating trusted buffers, insider access, and user complacency, ultimately compromising legitimate transactions and privacy.
Real-World Scenarios of Shared Wallets Backfiring
Shared wallets, while convenient, can produce tangible problems when trust boundaries blur and access permissions are mismanaged. In real-world cases, small lapses expand: accidental disclosures, changed partnerships, or revocation delays allow unauthorized moves. Privacy lapses emerge when logs or notifications reveal sensitive patterns. Social engineering exploits misperceived trust, prompting transfers or access grants before verification completes. Freedom demands disciplined, verifiable practices to prevent backfires.
Practical Safeguards to Protect Your Wallet
Practical safeguards begin with strict access control and clear ownership, ensuring that permissions align with documented roles rather than informal trust. The approach emphasizes least privilege, multi-factor verification, and regular audits to minimize privacy loopholes.
Continual monitoring detects anomalies, while transparent policies clarify responsibilities. Education on data handling supports intentional sharing, reducing risk without limiting legitimate collaboration or personal autonomy in digital spaces.
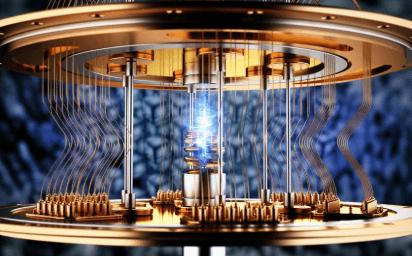
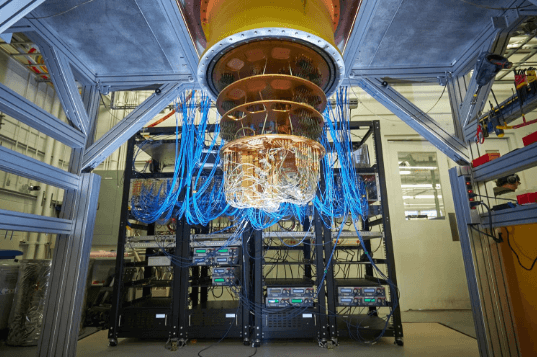
See also: Quantum Computing: Beyond Classical Limits
Frequently Asked Questions
How Can Shared Wallet Info Affect Family Members?
A shared wallet can expose family members to privacy breaches and identity theft, as exposed credentials may be misused by others. Cautious handling protects heirs’ financial security, minimizes risk, and preserves freedom to manage personal affairs independently.
What Legal Risks Come With Sharing Wallet Details?
The legal risks with sharing wallet details include potential privacy violations and liability if unauthorized transactions occur; entities may pursue recovery through civil actions. Data storage risks amplify exposure, demanding vigilance, consent, and robust protective measures for freedom-focused users.
Can Medical Debts Arise From Compromised Wallet Data?
Medical debts can emerge from compromised wallet data, underscored by privacy lapses that expose identities to theft. The narrative warns: identity theft shadows finances, while medical bills cascade, prompting cautious, freedom-seeking individuals to protect sensitive information and monitor accounts.
Do Employers Monitor Financial Data You Share?
Employers typically do not indiscriminately monitor personal financial data; however, certain programs and compliance requirements may allow limited employer monitoring of financial information. The privacy consequences depend on policies, consent, and applicable laws, shaping personal financial freedom and boundaries.
Are There Risks From Minor Discrepancies in Balances?
The answer notes that minor discrepancies can occur, but they matter; digital verification depends on accuracy. It emphasizes data minimization, financial privacy, and wary caution, while irony underscores how freedom-minded individuals still demand reliable figures.
Conclusion
Within the high-stakes realm of shared wallet information, risk compounds quickly when access is broadly granted. A telling statistic: as few as two trusted collaborators can, through any lapse, enable unauthorized transfers in minutes, underscoring the fragility of shared trust. The takeaway is clear—strict least-privilege access, enforced MFA, and auditable, transparent sharing practices are essential. In cautious, measured steps, stakeholders should continuously monitor permissions and rapidly revoke access when doubt arises.